Every time you browse the internet, your device leaves behind information.
Websites can see your IP address, your approximate location, the network you use, and sometimes even details about your browsing behavior. Most people never think about this because the process happens silently in the background.
But for businesses, developers, marketers, researchers, and privacy-conscious users, exposing this information directly can become a serious limitation.
That is where proxies come in.
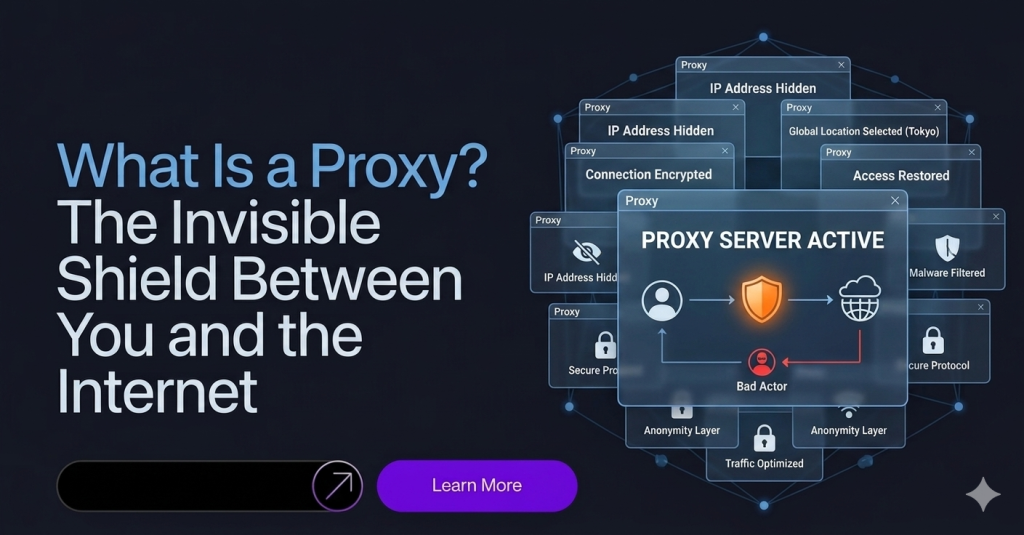
A proxy acts like a middle layer between you and the internet. Instead of connecting directly to a website, your traffic first passes through another server, which then forwards the request on your behalf.
To the website, the proxy appears to be the visitor instead of you.
This simple concept powers a massive part of today’s internet infrastructure, from cybersecurity and privacy protection to web scraping, automation, ad verification, SEO monitoring, and global content access.
Although proxies operate quietly behind the scenes, they have become one of the most important tools in the modern digital world.
Understanding How a Proxy Works
Normally, when you visit a website, your device connects directly to the server hosting that site.
The request contains information such as:
- Your IP address
- Your location
- Your internet provider
- Device and browser data
The website responds directly back to your device.
A proxy changes this flow completely.
Instead of your device contacting the website directly, the request first travels to a proxy server. The proxy then sends the request to the target website using its own IP address instead of yours.
The website only sees the proxy.
Once the website responds, the proxy forwards the data back to you.
The entire process usually happens within milliseconds, making it almost invisible to the end user.
Why Proxies Matter Today
Years ago, proxies were mainly associated with privacy and anonymous browsing.
Today, their role is much bigger.
Modern websites actively monitor visitors, track browsing behavior, limit access, block automated systems, and enforce regional restrictions. At the same time, businesses increasingly depend on data collection, automation, and global access to stay competitive.
Proxies sit at the center of this ecosystem.
Without them, many online operations would simply stop functioning effectively.
Companies now use proxies for:
- Web scraping
- SEO monitoring
- Ad verification
- Price comparison
- Cybersecurity
- Brand protection
- Social media management
- Automation workflows
- Market research
- Bypassing geo-restrictions
Even everyday users rely on proxies indirectly through VPNs, content delivery systems, and enterprise security networks.
The Difference Between a Proxy and a VPN
Many people confuse proxies with VPNs because both hide your IP address.
However, they work differently.
A proxy usually routes traffic from a specific application or browser. It changes how requests appear to websites but may not encrypt all internet traffic.
A VPN, on the other hand, creates an encrypted tunnel for your entire internet connection.
In simple terms:
- A proxy primarily changes identity
- A VPN focuses more on secure communication
Businesses running scraping or automation systems often prefer proxies because they offer greater flexibility, scalability, and location targeting.
Types of Proxies
Not all proxies are the same.
Different proxy types serve different purposes depending on speed, anonymity, reliability, and detection resistance.
Datacenter Proxies
Datacenter proxies come from cloud servers or hosting providers rather than real internet users.
They are fast, affordable, and widely available.
However, websites can often identify datacenter IP ranges easily because they originate from hosting infrastructure instead of residential internet providers.
This makes them more likely to get blocked on heavily protected websites.
Datacenter proxies are commonly used for:
- High-speed scraping
- Bulk automation
- Performance testing
- Low-cost tasks
Residential Proxies
Residential proxies route traffic through real devices connected to genuine residential internet networks.
This makes them appear much more natural to websites.
Because the IP addresses belong to actual users and internet service providers, residential proxies are significantly harder to detect.
They are widely used for:
- Web scraping
- Ad verification
- Ecommerce monitoring
- Sneaker automation
- Multi-account management
- Geo-targeted browsing
Residential proxies are slower and more expensive than datacenter proxies, but they offer much higher trust levels.
Mobile Proxies
Mobile proxies use IP addresses assigned by mobile carriers.
These are considered some of the most trusted IPs online because mobile networks naturally share IPs across many real users.
Mobile proxies are especially effective for:
- Social media automation
- Mobile app testing
- Account management
- High-trust browsing environments
However, they are usually more expensive and have limited availability compared to other proxy types.
ISP Proxies
ISP proxies combine characteristics of both residential and datacenter proxies.
They are hosted on servers but registered under internet service providers, making them appear more legitimate than standard datacenter IPs.
They offer a balance between speed and trust.
How Websites Detect Proxies
Modern websites have become extremely sophisticated at identifying proxy traffic.
Simply hiding your IP address is no longer enough.
Security systems now analyze:
- IP reputation
- Browser fingerprints
- Request behavior
- Session consistency
- TLS signatures
- Traffic patterns
Large platforms such as Cloudflare and Datadome actively score traffic to determine whether a visitor appears legitimate.
For example, if hundreds of accounts suddenly log in from the same proxy network with identical browser fingerprints, detection systems can flag the activity instantly.
That is why modern proxy usage often requires browser fingerprint management and realistic browsing behavior alongside IP rotation.
Proxies and Web Scraping
One of the biggest uses of proxies today is web scraping.
Businesses rely on public web data for:
- Competitor monitoring
- Pricing intelligence
- SEO tracking
- Market analysis
- Trend forecasting
Without proxies, scraping large websites becomes extremely difficult because repeated requests from one IP quickly trigger rate limits or bans.
By distributing requests across multiple IPs, proxies allow scraping systems to collect data more naturally and efficiently.
However, modern scraping is no longer just about rotating IPs.
Websites increasingly analyze browser fingerprints and behavioral signals to detect automation. This means successful scraping often depends on combining proxies with realistic browser environments.
Proxies and Privacy
For everyday users, proxies offer an additional layer of privacy.
When browsing through a proxy:
- Websites cannot directly see your real IP
- Your location becomes masked
- Tracking becomes more difficult
- Public Wi-Fi exposure can be reduced
While proxies are not complete privacy solutions by themselves, they help minimize direct exposure online.
Journalists, researchers, and cybersecurity professionals often use proxies to separate their browsing identity from their real-world location.
Common Misconceptions About Proxies
Many people assume proxies are only used for illegal activity or hacking.
That is far from reality.
Most proxy usage today is completely legitimate and business-driven.
Large companies use proxies daily for:
- Cybersecurity testing
- Ad fraud prevention
- Brand monitoring
- Data collection
- Localization testing
In fact, much of the modern internet economy quietly depends on proxy infrastructure operating behind the scenes.
Another misconception is that proxies guarantee anonymity.
They do not.
A proxy only hides certain layers of your identity. Websites can still detect users through browser fingerprints, cookies, login behavior, and other tracking methods.
Choosing the Right Proxy
The best proxy depends entirely on the use case.
For high-volume speed-focused tasks, datacenter proxies may work well.
For stealth, scraping, and automation, residential proxies are usually more effective.
For mobile app environments or social media automation, mobile proxies often provide the highest trust level.
The key factors usually include:
- Speed
- Detection resistance
- Geographic targeting
- Reliability
- Session control
- Cost
Choosing the wrong type can dramatically increase detection rates and reduce performance.
The Future of Proxies
As websites become more advanced, proxies are evolving too.
Modern anti-bot systems now evaluate complete browsing identities rather than simple IP addresses. This means proxies alone are no longer enough for sophisticated automation.
The future is shifting toward full identity management systems that combine:
- Proxy infrastructure
- Browser fingerprint control
- Behavioral simulation
- Session persistence
- AI-driven automation
Proxies remain the foundation, but they are increasingly part of a larger ecosystem designed to create realistic digital identities.
Final Thoughts
A proxy is much more than a tool for hiding an IP address.
It acts as an invisible shield between users and the internet, helping manage privacy, access, automation, and digital identity.
From cybersecurity teams and data companies to marketers and everyday users, proxies have become deeply integrated into how the modern internet operates.
As online tracking and detection systems continue evolving, proxies are no longer optional tools for advanced users. They are becoming essential infrastructure for navigating the web safely, efficiently, and at scale.